Given the ubiquitous nature of information technology, anyone can pick up a computer, watch a tutorial, and start coding. This individual may then hone their skills via formal education or informal means such as boot camps and short courses, and eventually go on to create a career out of the skills they acquired. And despite having spent hours upon hours honing their development skills, they may have never picked up the skill of writing secure code. And this, would be no fault of theirs. We write code because it enables us to create programs that help us solve problems, because we enjoy the thrill coding gives us, and honestly it kind of makes us feel really smart (when the code actually works of course) – security simply is not the emphasis. This problem might also be systemic as formal education oft-times places too much emphasis on the basics of coding and may gloss over or entirely omit the fundamentals of secure code.
This lack of awareness and preparedness becomes a pickle when one codes in a professional environment, especially where there’s the added pressure of tight deadlines. They push out a new feature on a short timeline and unbeknownst to everyone, a security vulnerability has been introduced into their environment – ready for the world to exploit. Without the proper security posture, culture, and infrastructure, problems are bound to be left unchecked until it is too late.

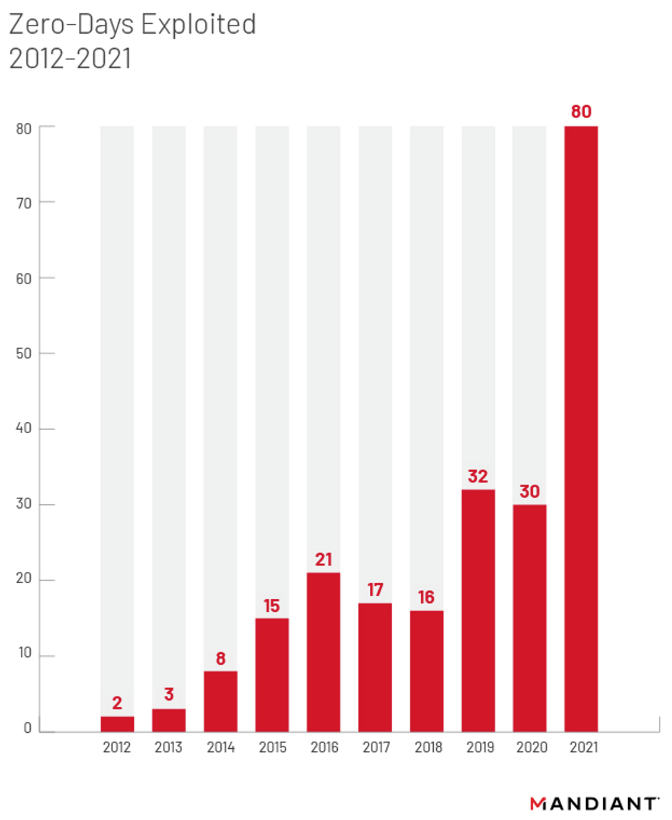
Based on an article from The Mandiant Threat Intelligence, 2021 saw a significant rise in zero-day exploitations. Just in the last year, Java developers found themselves rushing to patch two zero-day vulnerabilities; Log4Shell (CVE-2021-44228) and Spring4Shell (CVE-2022-22963).
There are several practical steps an individual can take to make ensure their code does not end up resulting in a security breach. A quick round on google will give you a list that might look like this:
- Always validate and sanitize user input
- Don’t hard code cryptographic keys or sensitive data
- Use appropriate headers in the response that make sure to only allow data that is desired
Organisations may aid in building this knowledge for their developers by providing them with a training platform. Checkmarx offers an interactive application security training platform that achieves this well. Their platform sharpens the skills that developers need to avoid security issues, fix vulnerabilities, and write secure code by letting them “wear the hacker’s hat” as they see all the moving parts of the application stack within the platform’s interactive lessons.
Having developers that are educated on application security is the first step, security tools and automation tend to be a more effective method to minimize the risk exposure of an organisation.
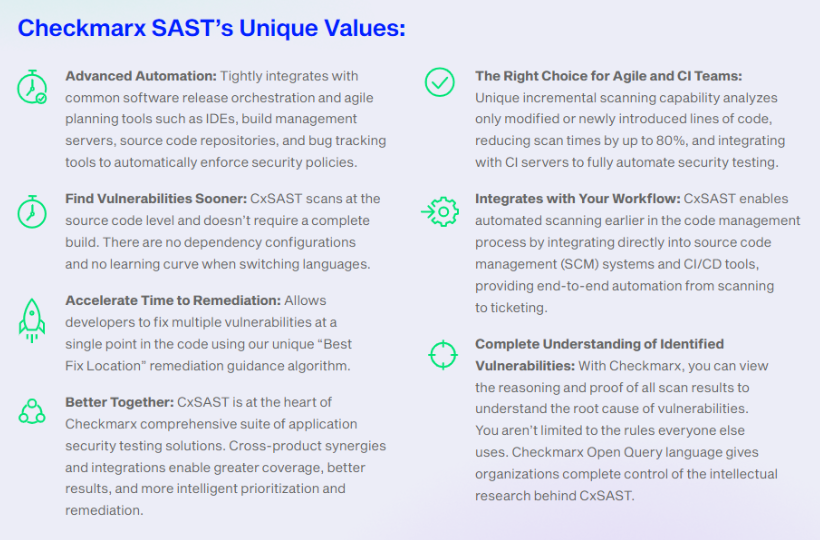
The first such security tool is a static source code analysis tool like Checkmarx Static Application Security Testing (CxSAST). CxSAST allows developers to run scans fast and often within a text editor of choice while they code. Developers do not have to concern themselves too much with the nitty-gritty of application security as the product will flag any potential vulnerabilities the application being built might have. CxSAST also goes as far as to provide a recommended fix for the results generated and suggests where is the best line to apply the remediation within your code.
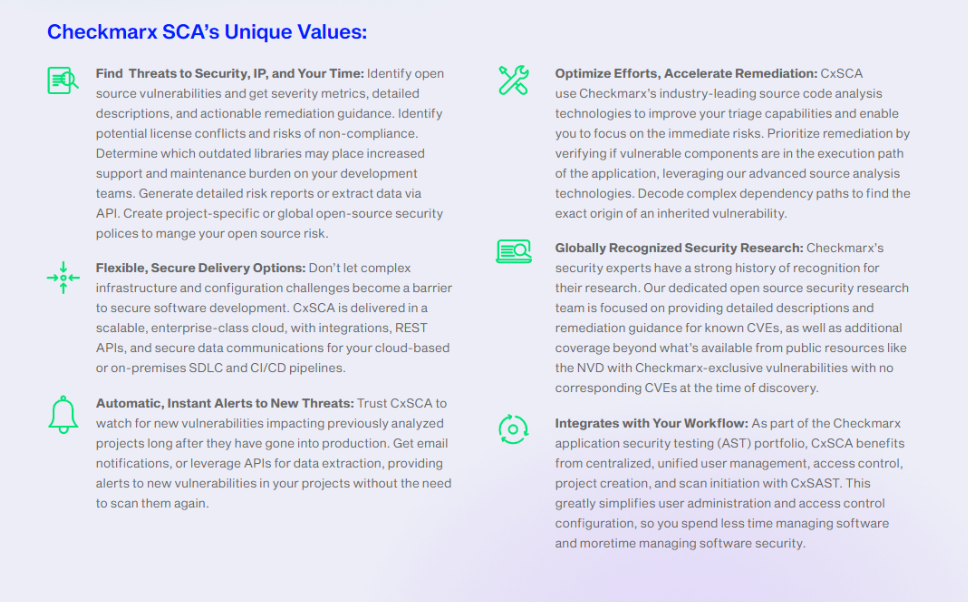
Another product recommended within any organisation’s security arsenal is a software composition analysis tool. An example of such a product is Checkmarx Software Composition Analysis (CxSCA). When developing an application, majority of the code tends to come in from open source libraries – allowing the developer to focus on achieving the business requirement. It is important to ensure that these libraries being pulled in do not introduce risks to the application. Checkmarx SCA addresses these issues by providing accurate, relevant, and actionable open source risk insight, backed by a dedicated open source security research team and seamlessly integrated throughout the software development life cycle.
Security should a priority for every developer and organisation. If there is an opportunity to improve the security posture of the organisation you work in, take it! Our Sales Team will gladly take on this journey with you, feel free to contact them at sales@netrust.net.
Follow us on LinkedIn for the latest happenings/updates.