Are you trying to implement or are you trying to understand Encryption from scratch? Or does your brain feel like scrambled eggs after trying to understand how S-boxes work in the AES algorithm with GCM mode? In this article, we aim to explain Encryption by using real life objects and examples to bridge the concept to reality.
Let’s start with a primer video, where we will use letter wax seals to demonstrate what a digital signature is.
Now that you know what encryption is, let’s fill in the remaining information you will need to know to work with it. Don’t worry if the rest of the article seems technical, you just need to know enough to select the most suitable components for your use case.
Use Cases and Algorithms
There are two types of encryption algorithms, symmetric and asymmetric. For ease of understanding, symmetric algorithms use the same key for encryption and decryption, whereas asymmetric algorithms use a key pair instead. A key pair (consisting of a “private key” and “public key”) can be imagined as a digital conjoined twin, tightly bound to each other at birth, with one half used for encryption and the other half for decryption.
They are suitable for different purposes. When considering encryption, it is recommended to start with a symmetric algorithm as the base. They are fast and can handle any amount of data.
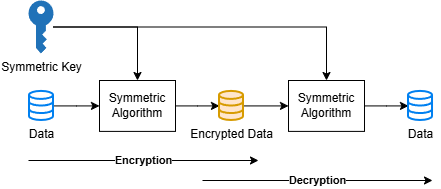
This approach is typically enough for most use cases where the intention is to encrypt data to transfer to the archive, or to another internal application. It is expected that the internal application will have the means to use the same key or a securely shared copy of it to decrypt the data.
For transfer to external parties, the same approach could technically work so long as the key can be securely and secretly shared with the external party. It would not do, for example, to send the key via email. Alternatively, asymmetric algorithms would serve well in this scenario.
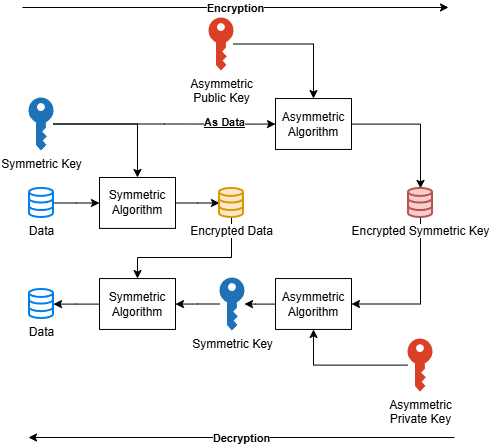
This approach covers the remaining use cases in which encrypted data needs to be sent out. You will need to get hold of the recipient’s public key or digital certificate if they have it. Yes, it is the same digital certificate used for digital signatures.
Now, which actual algorithm do we go with? Typical industry standard is to use the best open standard algorithm at the time, which is AES for symmetric and RSA/ECC for asymmetric at the point of writing. These algorithms have been thoroughly analysed by the community. Do avoid the trap of thinking of using an obscure or custom algorithm, they add risk without necessarily adding strength to the equation.
Also, ensure that some crypto mode is used together with the symmetric algorithm. The strongest available today unencumbered by patents, is GCM. If some of the legacy components in the ecosystem are unable to handle that, CBC is a good fallback. Do avoid ECB as that is effectively running without a mode.
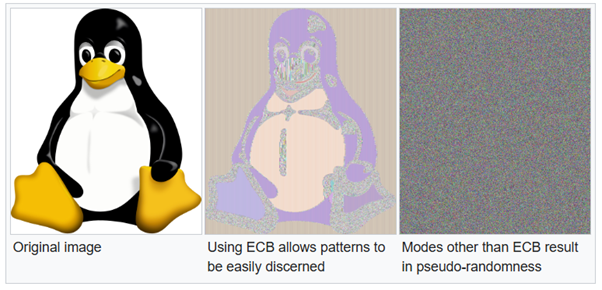
The reason is best explained by this image from Wikipedia [1]. Modes add some jitter into the process so that each time the encryption process is run, different results are produced with the same source data. Yet it is still able to decrypt back to the original source data.
Key Generation and Storage
We have talked about the keys used in symmetric algorithms above. Needless to say, it should be securely generated using a secure random byte generator and access to it should be restricted except for the application doing the cryptographic processes.
The keys need to be rolled over periodically as well. This means old keys are archived (not deleted!) and new keys generated to use on future data encryption. As the encrypted data needs to be accessible in the future, the old keys need to be stored for as long as the data remains in the picture. In some use cases we have seen, this could be 7 years, or as long as 99 years.
For the best security it is recommended to generate and retain the key within a Hardware Security Module (HSM) as it provides both the generation and storage facilities in one hardware package. There are also means to securely backup and restore the keys in the event of disaster recovery or migration to other environments. If your application is on Cloud, there are HSM equivalents or Key Management Services (KMS) which serve a similar role on the major Cloud providers.
For asymmetric algorithms this is not an issue, as public keys or digital certificates are designed to be shared to the party that wishes to encrypt data for you.
Implementation and Applications
Theory is all fine and dandy, but the devil is in the (implementation) details. Cryptography is one of those things where one critical misstep could render the process meaningless. For example, if the encryption key is sent out via an insecure process, it compromises all past and future data encrypted using that particular key.
There are off the shelf applications that can handle the encryption process, but these typically only cover a specific use case or ecosystem. One example is email encryption (S/MIME) through Microsoft Outlook.
For other cases, especially if encryption is required for your application’s data, a custom solution should be expected. This may use an existing cryptographic API product or library, or may be made to measure entirely.
Conclusion
There is a lot more to know under the hood, but contrary to common belief, you do not need to know everything to work with data encryption. What we have laid out above should be sufficient to get you started, though it is strongly recommended to seek a consultation to determine the best solution for your requirements. We are also including answers to some frequently asked questions below that we have encountered before.
Netrust has been a trusted cybersecurity partner and solutions provider since 1997. We have decades of experience in end-to-end cryptographic processes, including encryption and decryption. Every bit of experience we have builds up to the megabytes of confidence you can place in us. Contact us today for a consultation on your encryption needs.
FAQs
- Can I encrypt just a section of the data?
Certainly. Off the shelf applications would not support this, though so the custom implementation would have to be able to cut, encrypt and piece the data blocks back together as required.
- I have already encrypted a file, but then I lost my key/token! What should I do?
The first step is to determine how the key/token was lost. If there are reasonable grounds to believe it has been compromised, you will need to assume that all data encrypted with the lost key is compromised and respond in accordance with your country’s data privacy guidelines, such as the PDPA.
If the key is not compromised, you can look into restoring the key from backup. This should already be defined in the disaster recovery procedures before the system goes live. If the keys are not backed up or cannot be restored, then access to the data is effectively lost.
There is no convenient backdoor to restore access, this is exactly how cryptographic systems are intended to work.
- Can someone else see the data?
No, encrypted data is effectively scrambled. The only way anyone can see the original data is if they know the correct algorithm, modes, and processes that the file is encrypted through, and have the correct key to run said decryption process.
- I am sending the data to an external party; how can they confirm that this data came from me?
Encryption does not carry the sender’s identity. To achieve this, the data can be digitally signed first before it is encrypted and sent. The digital signature (Read up more on our article on Explaining Digital Signatures through real world examples) will carry the sender’s identity.
- Can digital signatures and encryption be used together?
Certainly, they are not mutually exclusive.
- Can someone else tamper with the data?
It is not possible to edit the data without corrupting the original. What that means is once edited, decryption can still be attempted, but the original data cannot be reconstructed. What is likely to emerge would be gibberish data.
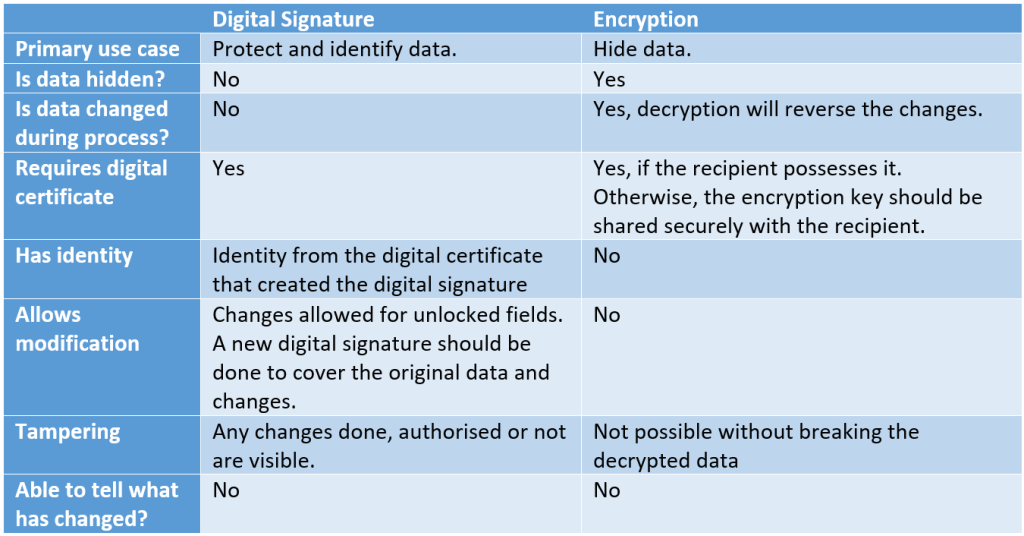
Reference table on the differences between Digital Signatures and Encryption.
[1] Image source: https://en.wikipedia.org/wiki/Block_cipher_mode_of_operation#ECB
Follow us on LinkedIn for the latest happenings/updates.